🔐 Symmetric Encryption as a Shared Spice Code
You and your partner are crypto-chefs working out of a hidden culinary lab — no menus, no recipes shared, just encrypted flavor transmissions through rice and spice.
One day, your task is clear: take a boring bowl of plain rice (plaintext) and transform it into something so seasoned (ciphertext), only those with the exact spice formula (key) can taste-decode it.
This isn't your grandma's cookbook — this is culinary cryptography, and symmetric encryption is your shared secret sauce.
🧂 Encrypting the Message (Cooking the Ciphertext)
Challenge Mode Activated 🧠💥 You're standing in the covert corner of your culinary lab. Before you: a lifeless bowl of rice. Your mission? Encrypt it into flavour — so rich, only those with your signature spice blend can decode it.
👨🍳 Step-by-Step Breakdown:
🍚 Plain rice = Plaintext. This is your raw message. It's bland. Unprotected. Anyone could poke around and taste the data.
🧂 Season it with the Shared Spice Blend = Symmetric Key. You grab the mix — the exact ratio of herbs and heat that only you and your partner know. This is the key, used to transform the meal.
🔐 Encrypted dish = Ciphertext. Now the rice bursts with flavour, complexity, and mystery. Outsiders can't reverse-engineer it — unless they have the key. Otherwise? It's just a confusing bowl of mystery.
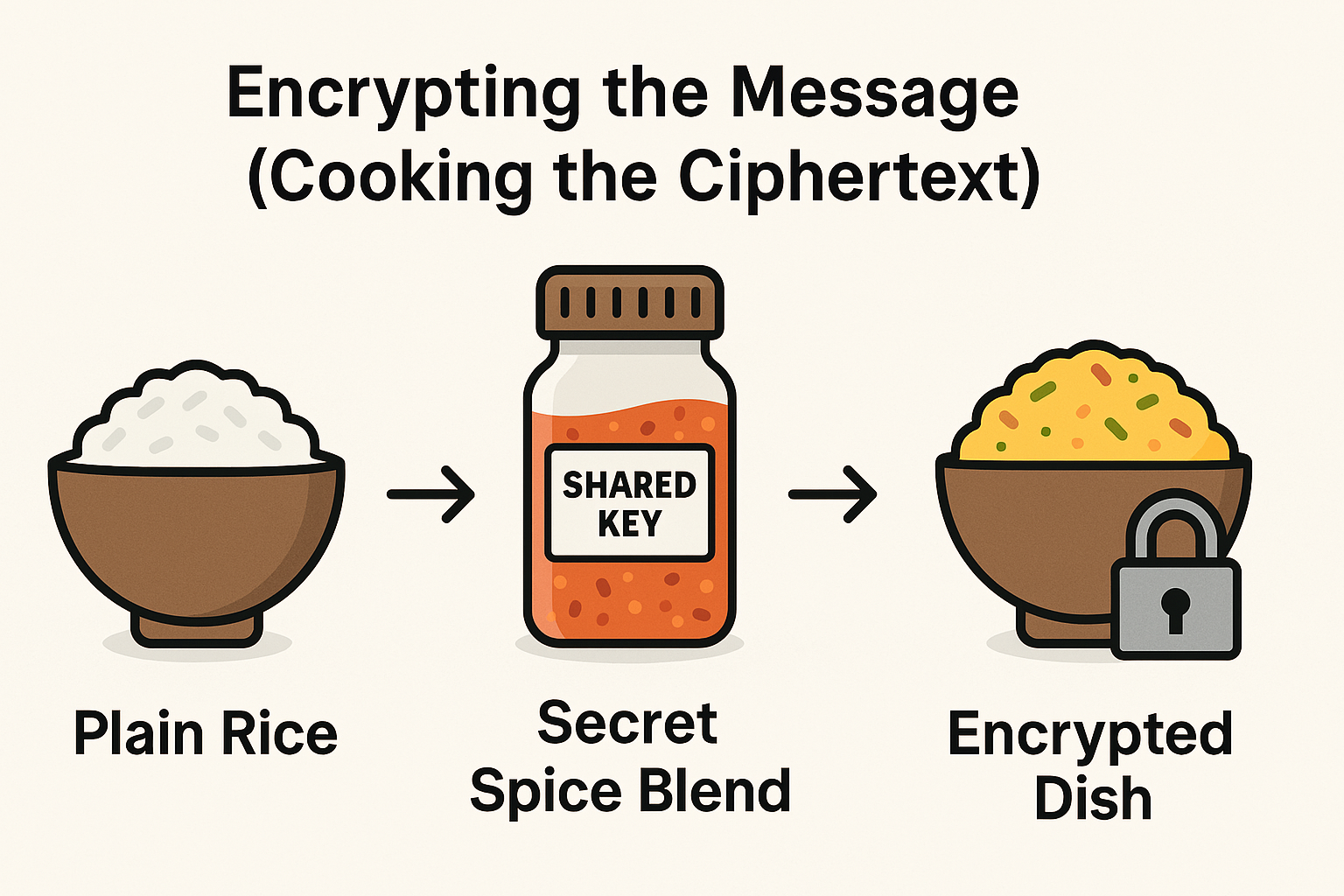
TIP: Think of the seasoning process like AES in action — it doesn't just sprinkle flavor, it stirs it deep into every byte of rice.
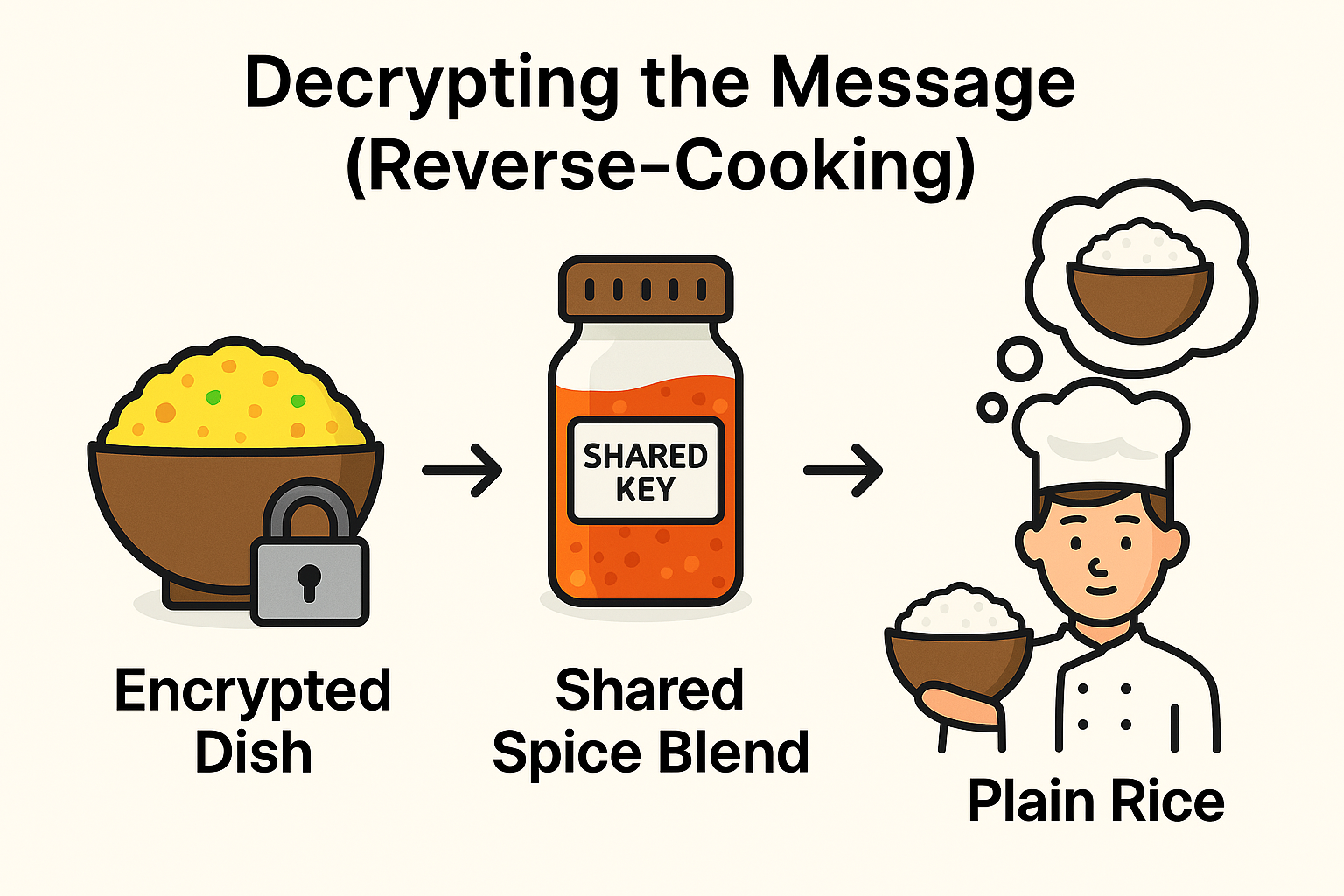
🍽️ Decrypting the Message (Reverse-Cooking)
MISSION UPDATE: The encrypted dish has reached your partner. No instructions. No label. Just spice-packed ciphertext, steaming and mysterious. Time to reverse-cook — reconstructing every byte of flavor using the one thing that makes it possible: your shared spice blend
🧪 Step-by-Step Reconstruction:
👭 The trusted partner receives the dish Not just any foodie — this is your fellow crypto-chef. He trained alongside you. He has the exact blend memorized.
🔍 Taste-decoding with the shared key. He take one bite… and boom. Every spice ratio, herb placement, and savory note clicks into place. Because he hold the same symmetric key, the ciphertext unravels into the original plaintext — grain by grain.
🛑 No key = broken flavor Anyone else? He might guess cumin instead of coriander, or drop too much salt. The result? Corrupted ciphertext. Ruined dish. Failed decryption.
Insight 🔎 Symmetric decryption isn't guessing — it's precision. AES and similar algorithms reverse the transformation only if the exact key is applied. Anything else scrambles your data like mistaking cinnamon for chilli powder.
🧠 Why It Works (Behind the Flavour)
The spice blend doesn't just taste good — it's a method. Symmetric encryption is all about precision, consistency, and trust between chefs who know exactly what they're serving.
🔑 Cryptographic Principle
- Shared key
- Encryption & decryption symmetry
- Confidentiality
- Integrity
5. Speed
🧪 How Tamper Protection Works
Add one wrong spice? It's game over. With symmetric encryption, even a single bit flipped during transmission leads to a completely different flavor — undetectable, unpredictable, and unusable.
👨🍳 Culinary Analogy
- You and your partner use the exact spice blend
- Same recipe going in — same taste coming out
- Only key-holders can prepare or identify the dish
- Tampering ruins the flavour, just like corrupted ciphertext
- Cooking is fast when the recipe's memorised
💥Integrity in encryption is like seasoning accuracy — off by one pinch, and the message goes bitter.
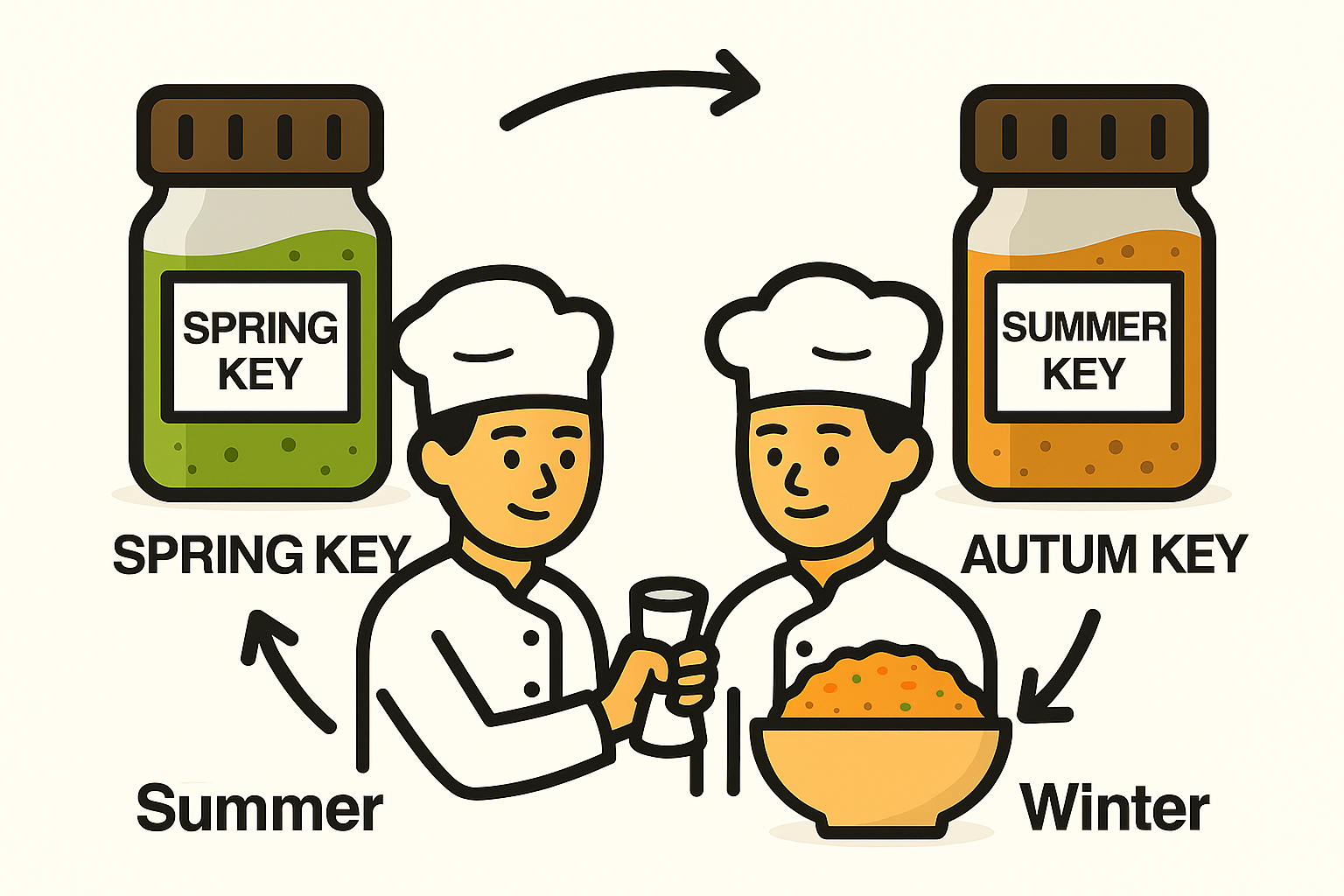
🍂 Bonus Layer: Key Rotation = Seasonal Menu
Even the most legendary spice blend ages. True crypto-chefs know: security gets stale unless refreshed. That's why you and your partner rotate your encryption keys like seasonal menus — changing flavors to keep the system fresh, unpredictable, and secure.
🍃 Why Rotate Your Key?
🧂 Old blends attract attention. Overused keys are like overhyped recipes — eventually, someone tries to reverse-engineer them.
🌦️ Seasonal flavours match seasonal risks. In winter, you might beef up your blend (security). In summer, keep it light but still encrypted.
🔁 Rotation means reduced exposure. A compromised key only affects recent dishes, not your whole cookbook.
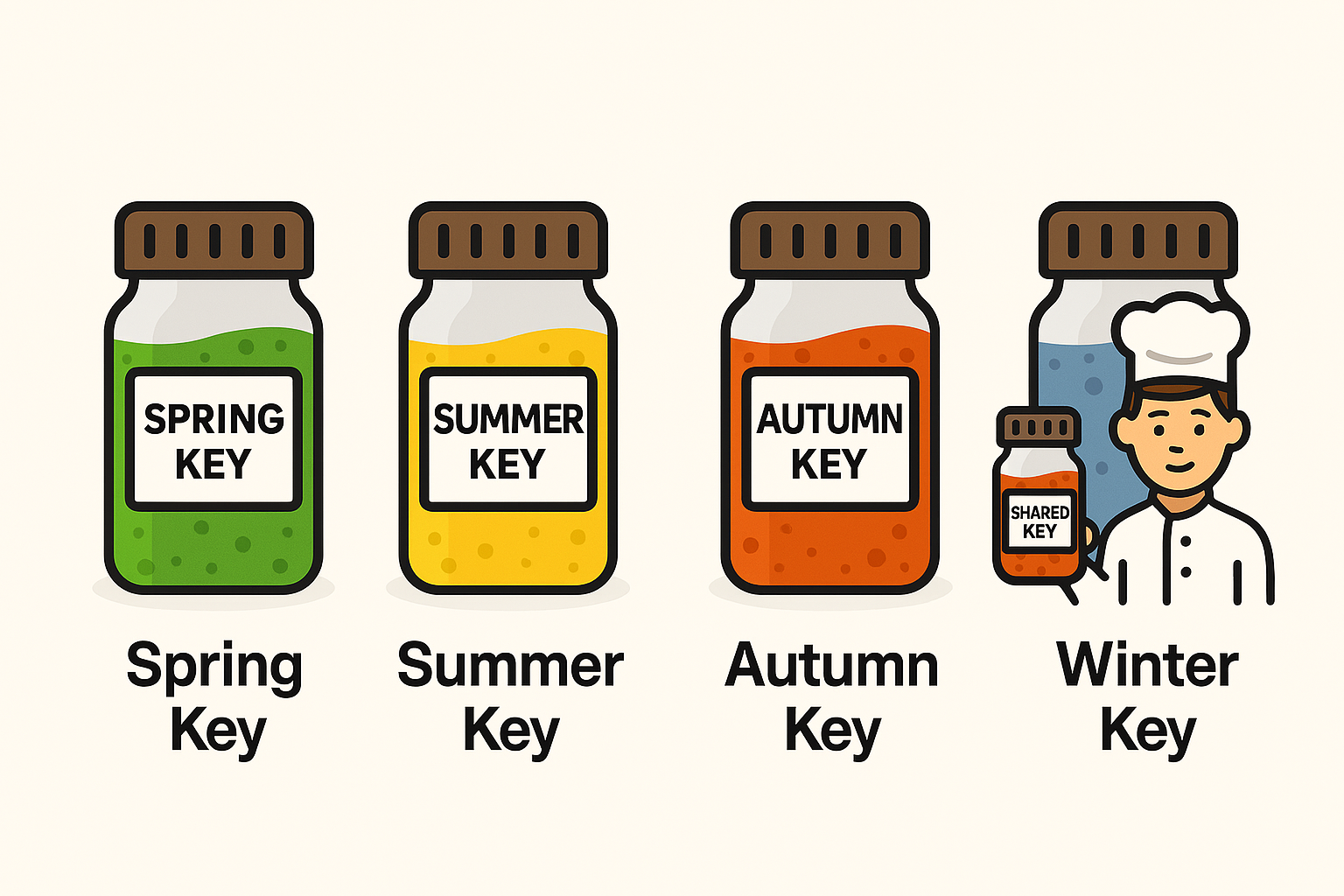
🔄 How It Works (Analogy Edition)
You swap out your shared spice jar every quarter. Spring's mix might be lighter and fresh — mint, lemon zest, a whisper of cumin. Autumn rolls in and you switch to bold, layered heat — paprika, chili, garlic.
But one thing never changes: only you two know the recipe.

🧂 Room: Secret Recipe -Symmetric Encryption Through Flavour
🔓 Welcome, agent. Your mission is clear: crack the code behind symmetric encryption — not through signal flow diagrams, but through the bold language of culinary secrecy. Flavour is your cipher. Timing is your key.
(Check at the bottom of the page : "Answer Reveal Section " to verify your answers )
🧪 Task 1: The Shared Spice Blend
"You can't cook the message unless you've got the secret seasoning."
Scenario: You and your cryptographic culinary partner operate from a hidden kitchen. Together, you crafted a covert spice blend — the perfect ratio of heat, complexity, and flavour. This blend is your shared key. Not even the sous chefs know the recipe.
🔑 Key Concept: Symmetric encryption uses the same key to encrypt and decrypt.
📝 Short-answer:
What's the name of the secret recipe shared between both chefs?
➡️ Expected answer: --- ------ ---
🍚 Task 2: Seasoning the Message
"Plain rice becomes encrypted poetry with the right spice."
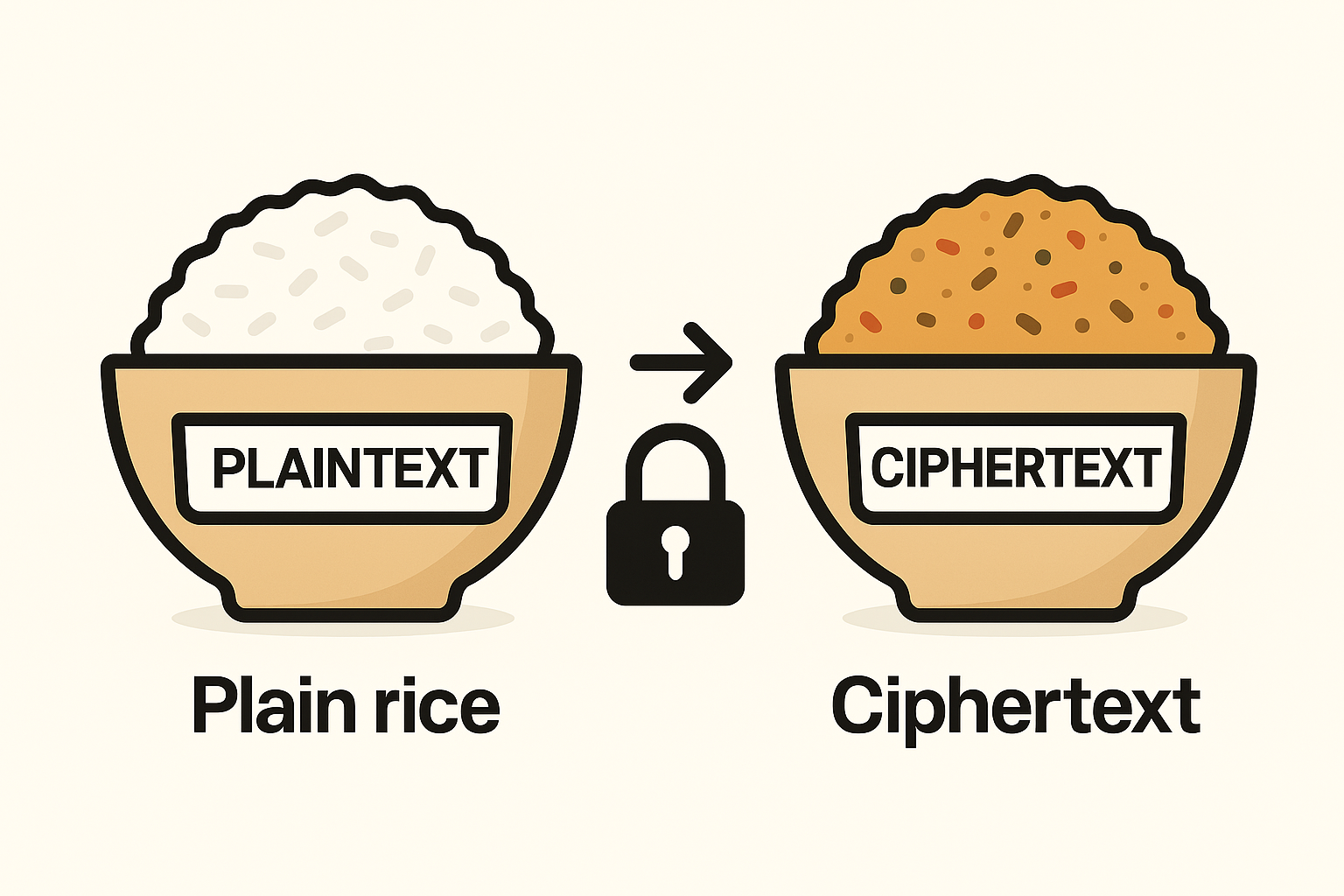
Scenario: Your plaintext is a dish of plain rice. You season it with the shared blend, transforming its flavour into ciphertext—rich, layered, and unreadable to outsiders.
🔐 Key Concept: Encryption obscures plaintext using a secret key.
📝 Fill-in-the-blank:
When rice is seasoned with the secret blend, it becomes ________.
➡️ Expected answer: ----------
🧑🍳 Task 3: Tasting the Truth
"Only the tongue that knows the blend can decode the dish."
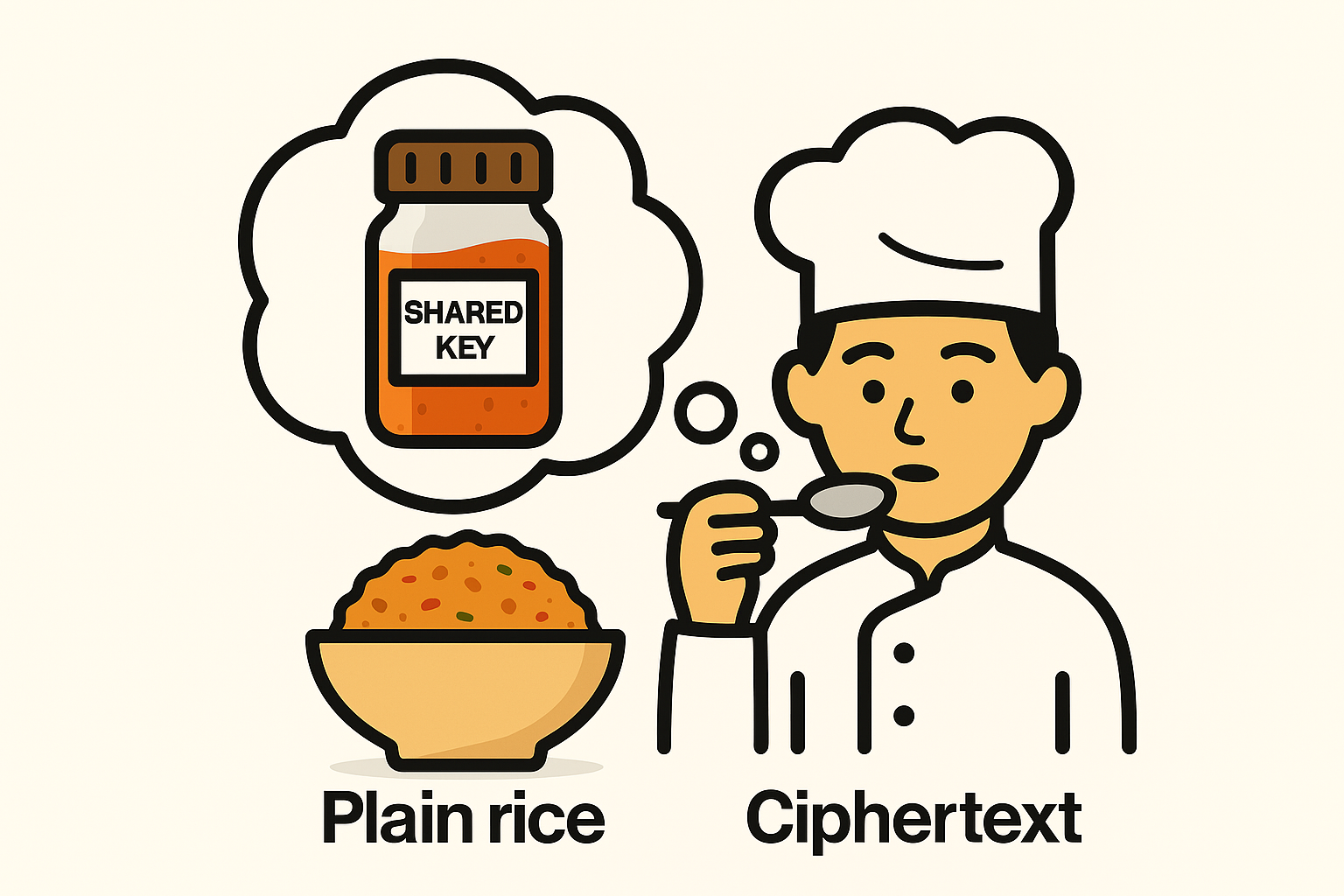
Scenario: Your partner receives the encrypted dish. With the shared spice ratios memorised, they decode the flavours, restoring the dish to its original state. Everyone else tastes confusion.
📌 Key Concept: Decryption reverses the encryption using the same key.
📝 Riddle-style question:
What secret ingredient allows the recipient to decode the dish?
➡️ Expected answer: --- ------ ----- -----
🗝️ Task 4: Key Exchange – The Original Recipe
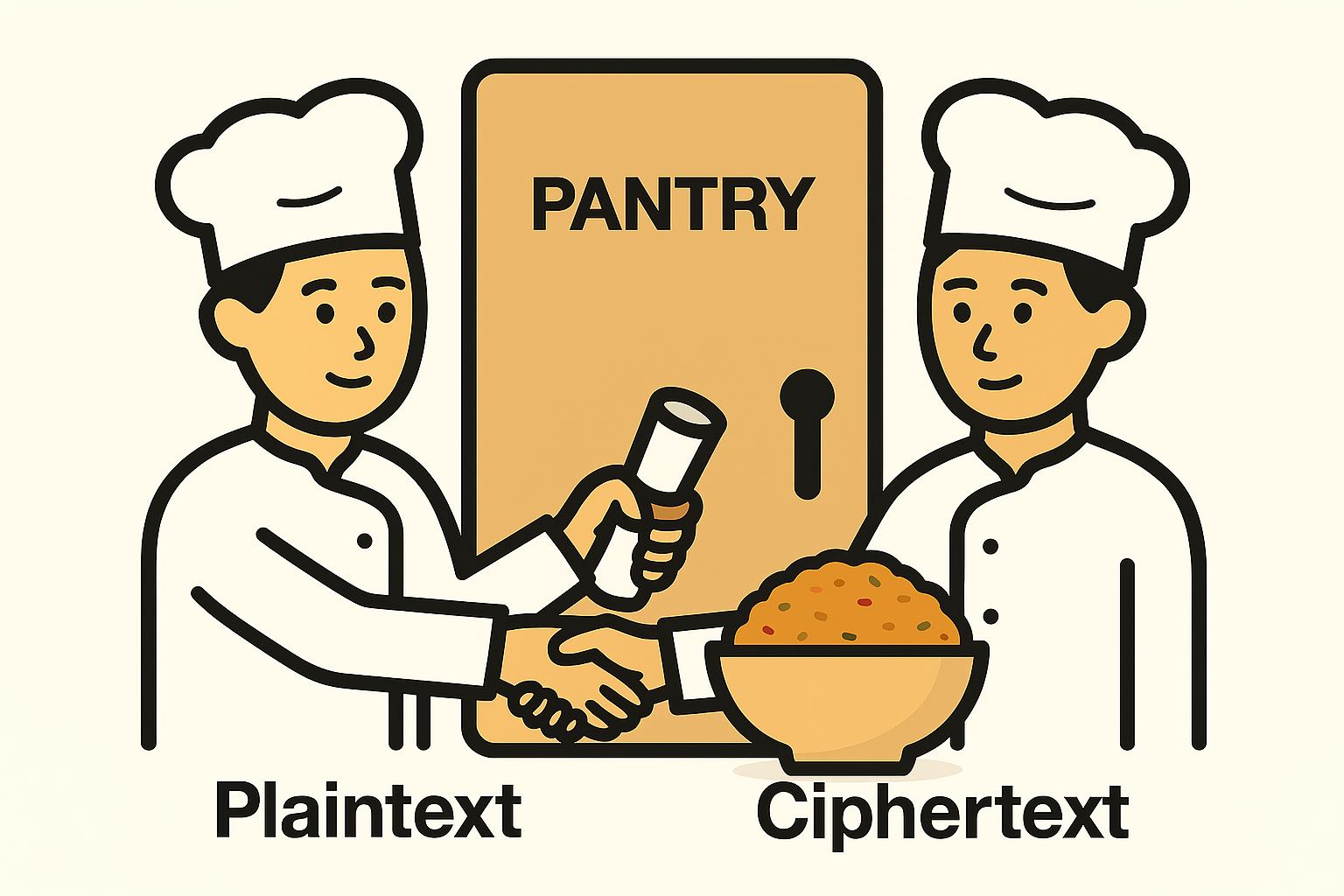
"Before the first bite, there was a handshake behind a pantry door."
Scenario: Before encrypting anything, you and your partner exchanged your spice blend securely. This key exchange protects your system from impostors and ensures flavour consistency.
🔒 Key Concept: Symmetric encryption requires a secure pre-shared key.
📝 Short-answer:
Why must the spice recipe be shared securely in advance?
➡️ Expected answer: -- ------ ---- ----- --- --- ---- --- --- ---------- --- ----------.
🔄 Task 5: Rotating the Blend
"Even the hottest spice loses its kick over time."
Scenario: To stay ahead of threats, you rotate the spice blend on a monthly basis. If someone compromised last month's recipe, your current dishes stay safe, because the flavour profile has evolved.
🌀 Key Concept: Key rotation prevents long-term compromise.
📝 Multiple choice:
What's a benefit of rotating the spice blend?
A) Prevents reused keys from being exploited
B) Makes the dish taste worse
C) Forces chefs to memorise ... nothing ...
➡️Expected answer: -
✅ Closing Statement
Flavor is trust. Encryption is precision. Keep your recipes secret, rotate your blends, and no one outside the kitchen will ever taste the truth.
Answer Reveal Section
✅ Mission Debrief: Secret Recipe Revealed
You've seasoned the rice, decoded the flavor, and rotated the blend. Ready to check your answers, agent? Let's see how sharp your tastebuds were.
🧪 Task Answers
🧂 Task 1 – The Shared Spice Blend: ✅ The shared key
🍚 Task 2 – Seasoning the Message: ✅ Ciphertext
👨🍳 Task 3 – Tasting the Truth: ✅ The shared spice blend
📦 Task 4 – Key Exchange: ✅ To ensure both sides use the same key for encryption and decryption.
🔄 Task 5 – Rotating the Blend: ✅ A) Prevents reused keys from being exploited
🎓 Flavour Level Scoring
Count your correct answers and find out your crypto-chef rank!
✅ Score Title Badge Emoji
5/5 Master Chef 🔥👨🍳🔐
3–4 Seasoned Apprentice 🌶️🧂
1–2 Needs More Salt 🫠🍚