Hash It, Smash It - Never Rehash It !
Discover the science of smoothies that can't be reverse-engineered — just like hashes.
Welcome to the blender bench of digital certainty. Here, ingredients become identity, flavors are fixed forever, and no sip tells the story of its mix…
🧃 Hashing as a Smoothie Blender for Identity

One Blend to Bind Identity. One Hash to Seal It.
Imagine you run a smoothie bar. Every time someone walks in and says their name, you toss their unique ingredients into the blender and spin up a smoothie. The final smoothie is always the same if they say the same name and ingredients , but it's impossible to reverse-engineer it into the exact fruit combination once it's blended.
That's what a hash function does:
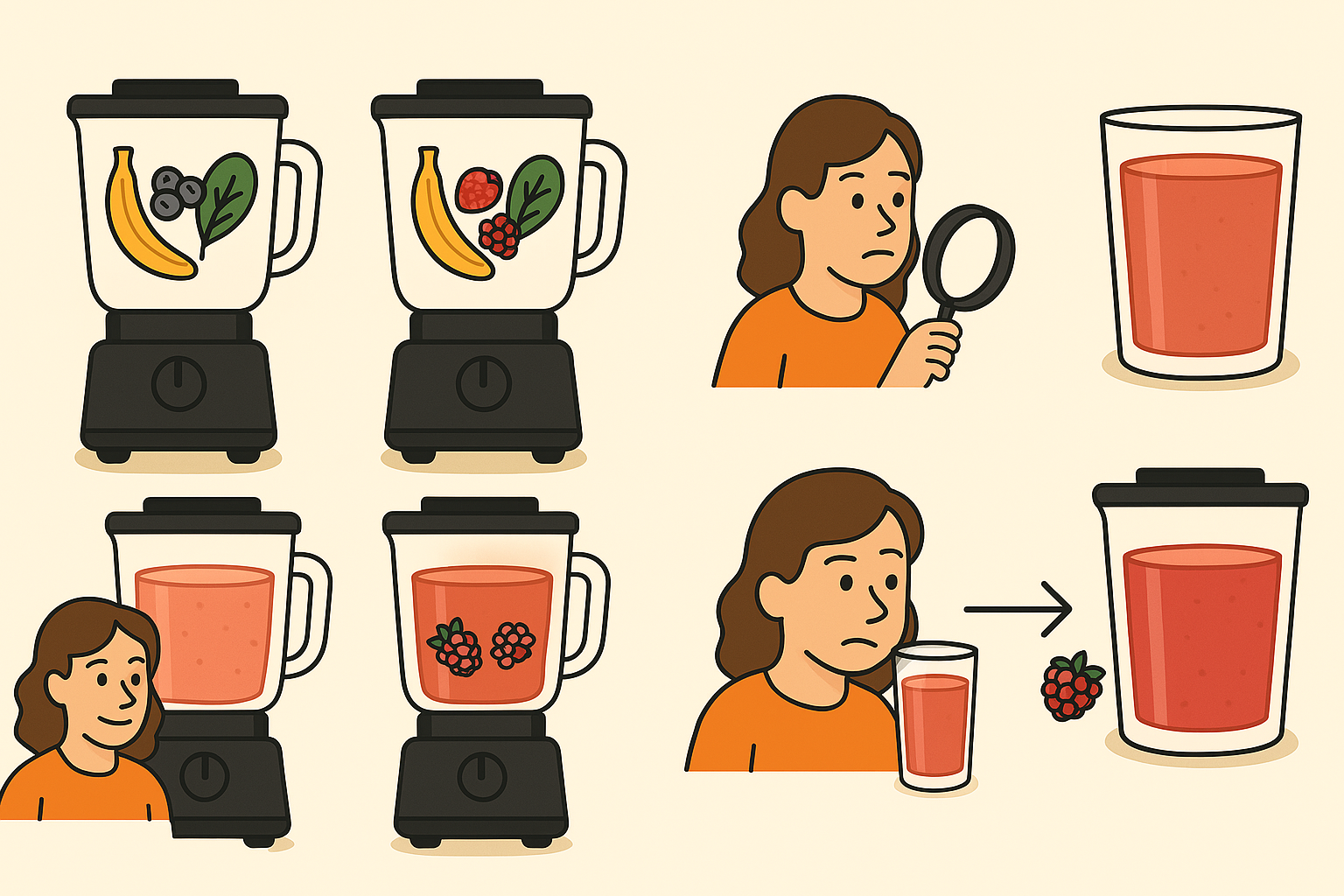
It takes an input, blends it into a fixed-length output (the smoothie), and ensures that
🧑🍳 Same input = same smoothie
The same input gives the same smoothie.
🍓 Different inputs = different smoothies
Different inputs produce radically different smoothies.
🔍 No reverse from smoothie → ingredients
You can't work backward from smoothie → ingredients.
💥 Tiny change = big output difference
A single tiny change (like one raspberry instead of two) makes the result totally different.
🪜 Hashing Breakdown in 5 Steps
🎯 Deterministic Output
If Alice always orders banana–blueberry–spinach, she'll always get the same smoothie colour, texture, and taste.
📌 In hashing: Same input → same hash.
🎨 Avalanche Effect
If Alice adds just one more raspberry to her mix, the resulting smoothie will look and taste wildly different.
📌 In hashing: Small change in input = drastically different hash.
🧊 Fixed Output Size
Whether Alice adds 3 ingredients or 30, her smoothie always fills an 8-ounce cup.
📌 In hashing: Variable-length input → fixed-length hash (e.g., SHA-256 = 256 bits).
🚫 One-Way Blending
Nobody—no matter how good they are—can taste the smoothie and extract the exact fruits used to make it.
📌 In hashing: You can't reverse a hash to find the original data.
🧑🤝🧑 Uniqueness with a Hint of Collision Risk
In theory, someone might unknowingly blend different ingredients and end up with the same-tasting smoothie. It's extremely rare, but technically possible.
📌 In hashing: Collisions are rare but possible (though cryptographic functions work to make them astronomically unlikely).
So here's the final sip, stirred with precision:
Hashing doesn't hide your data—it proves it's untouched. It doesn't lock doors—it leaves permanent marks on the handle so you know if someone's tampered with it.
You don't decrypt a hash. You compare it. Like scanning a fingerprint—not to see the hand, but to verify it's the same one that touched the vault yesterday.
🔐 Encryption's job?
Confidentiality.
It wraps your smoothie recipe in a padlocked cooler so only those with the key can peek inside.
💾 Hashing's job?
Integrity.
It records the exact taste without ever revealing what went into it.
Together, they're security's power couple:
You encrypt the message so only the receiver sees it.
You hash the message to prove no one touched it in transit.
You sign the hash to prove you're the one who mixed it.
Where does hashing work its magic?
🧩 Passwords — stored as hashes so even servers don't know them.
📝 Data integrity — verify a file's untouched with hash comparison.
🔏 Digital signatures — hash the content, sign the hash.
🛡️ Malware detection — hash known threats and block matches.
Hashing isn’t a mystery box. It’s a seal of truth. One input. One identity. One irreversible mark.
💾 Room: Smoothie Bar Secrets – Understanding Hashing
Welcome to the freshest smoothie bar in CryptoVale. You're here to learn the fine art of digital blending—where flavors are fixed and reversals are forbidden.
🍓 Task 1: The Smoothie Machine
"Same fruits in = same smoothie out."
Scenario:
Alice always gives the same name and blend: banana, blueberry, spinach. The staff blends it into her signature drink every time—no mistakes.
📌 Key Concept:
Hash functions produce the same output for the same input.
📝 Fill in the blank:
What ensures the same smoothie is created every time Alice orders the same combo? ------------- -------
🌀 Task 2: The Raspberry Twist
"One raspberry changes everything."
Scenario:
Bob orders almost the same thing as Alice—but adds a single raspberry. His smoothie tastes and looks totally different.
📌 Key Concept:
Hashing reacts dramatically to input changes.
📝 Multiple choice:
What describes how small input changes yield wildly different hashes?
A) Fixed Output Size
B) Deterministic Output
C) Avalanche Effect
D) One-Way Function
📏 Task 3: Smoothie Cup Size
"No matter how many fruits, the smoothie cup is always 8 oz."
Scenario:
Whether customers order 3 ingredients or 30, the bar always pours their smoothie into the same-sized takeaway cup.
📌 Key Concept:
Hash output is fixed length.
📝 True or False:
Hashes can vary in size depending on input length.-----
🔐 Task 4: One-Way Blending
"You can't sip a smoothie and tell what fruits were used."
Scenario:
Someone tries to reverse-engineer Alice's smoothie but fails. It's impossible to break down the blend into individual ingredients.
📌 Key Concept:
Hashing is non-reversible.
📝 Short answer:
What makes it impossible to retrieve the original input from a hash? Hashing is -------
💥 Task 5: Colliding Orders
"Two different fruit combos, one identical smoothie?"
Scenario:
Two customers order different blends, and by a one-in-a-trillion chance, the output smoothie tastes the same.
📌 Key Concept:
Hash collisions are extremely rare, but theoretically possible.
📝 Question:
What's the term for two different inputs producing the same hash? ---------
🎯 Final Task: Hashing vs Encryption
"You can drink a smoothie but not separate it. You can open a lock, but you need a key."
Scenario:
Encryption lets you unlock and view secret data if you have the key. Hashing doesn't care about keys—it's about permanent transformation.
📌 Key Concept:
Hashing = integrity & verification. Encryption = confidentiality & access.
📝 Quiz:
Which from above is reversible?
Quiz complete. Smoothie secure. Data untouched.
You didn't just stir fruit — you stirred function. You've seen how a single raspberry triggers chaos, how hashes whisper truth without telling secrets, and how encryption plays the quiet partner in the dance of integrity.
In the realm of cybersecurity, hashing is your proof, your receipt, your identity stamp. It won't lock the message, but it will shout if it's changed.
No keys. No reversals. Just a one-way blender of trust.
Ready to reveal what your blend says about your byte?
Let's unveil the hashes that stuck — and the badges you've earned.
🧃 Final Hashing Quiz Results: Smoothie Scoreboard
